Using SIEM Tools to Investigate a SOC Alert
I've been diving into SIEM tools to strengthen my cybersecurity skills and reinforce my IT fundamentals. Working with tools like Splunk and Microsoft Sentinel, I’ve learned how to collect and analyze logs, detect potential threats, and respond to security incidents. It’s been eye-opening to see how different systems generate logs and how those logs can reveal security risks. This hands-on experience has helped me better understand networking, system administration, and incident response—essential skills for my cybersecurity journey.

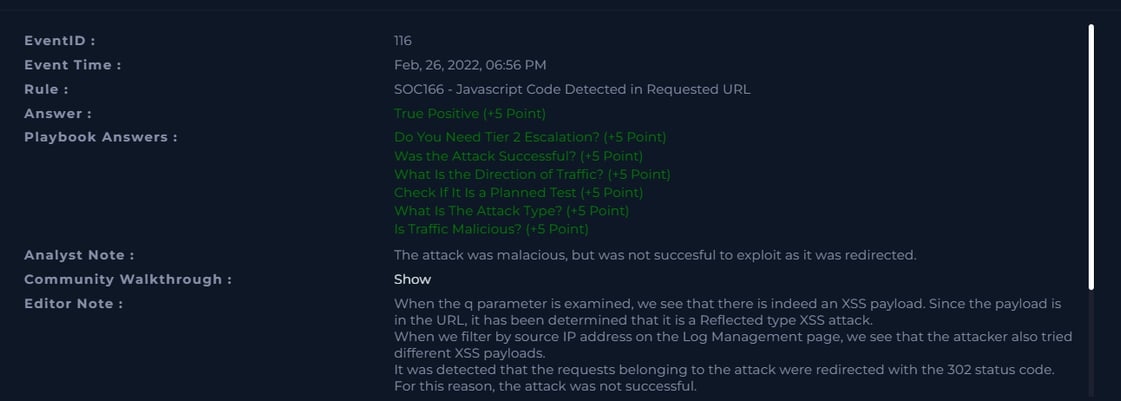
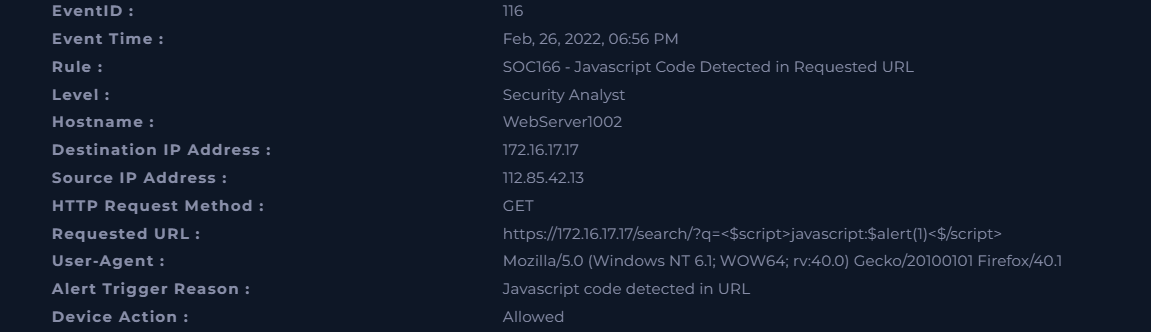
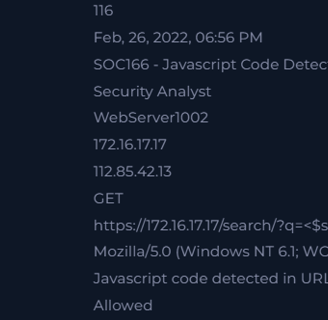
Here is the alert we will be investigating a SOC 166- Javascript Code Detected in Requested URL. Here are the details:
From this alert we can determine a few key details needed to fully investigate this alert.
When did the event happen? Feb, 26, 2022, 06:56 PM
What is the Source IP? 112.85.42.13
Destination IP? 172.16.17.17
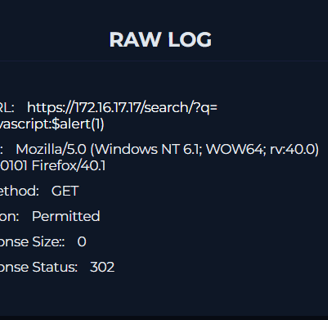
Requested URL? https://172.16.17.17/search/?q=<$script>javascript:$alert(1)<$/script>
User Agent: Mozilla/5.0 (Windows NT 6.1; WOW64; rv:40.0) Gecko/20100101 Firefox/40.1
Why did it alert? A possible XSS attack. We will figure it out once we investigate.
What was the HTTP request method? GET
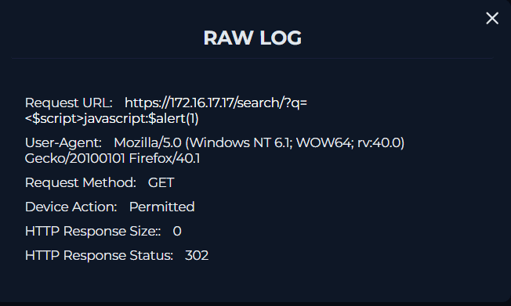
Using the Log Management tool in LetsDefend I entered the IP address 112.85.42.13 to track all logs relating to the event. I confirmed the exact log to the destination address 172.16.17.17, also including the URL https://172.16.17.17/search/?q=<$script>javascript:$alert(1)<$/script>. Here is the raw log:
The same IP address (112.85.42.13) made several requests to the destination IP address (172.16.17.17):
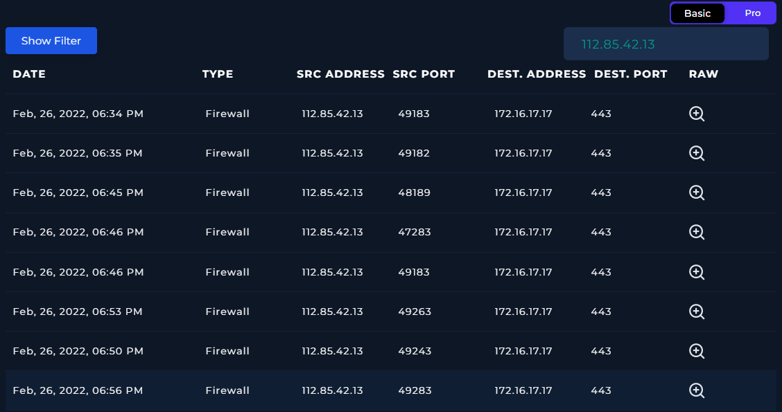
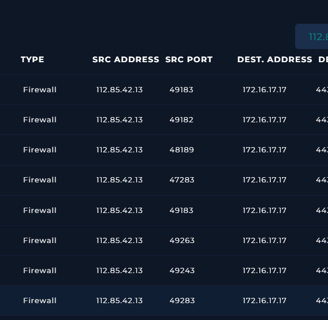
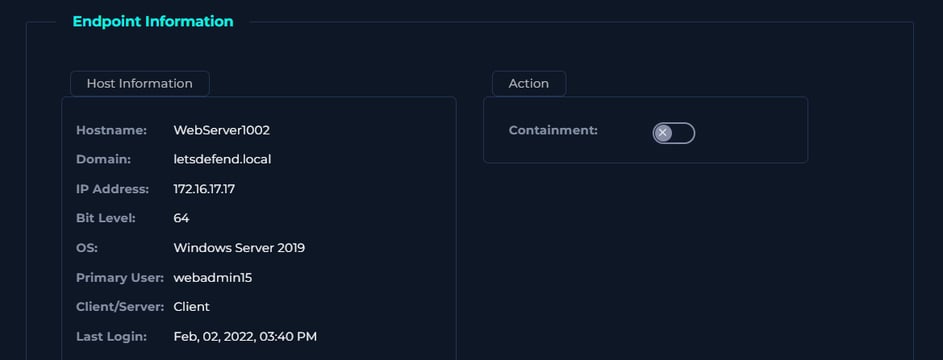
The IP address 112.85.42.13 did not come up in the EDR letting me know that the address is not within the network but the IP address 172.16.17.17 is within the network belonging to the hostname WebServer1002. We determined this information from the initial details given with the alert. (Refer to image 2)
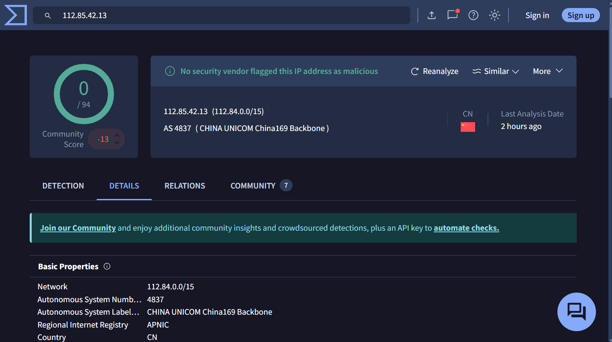
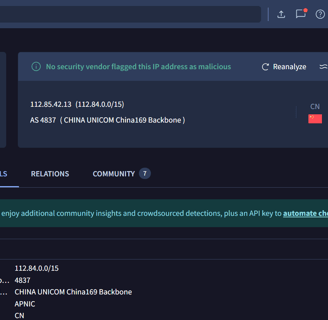
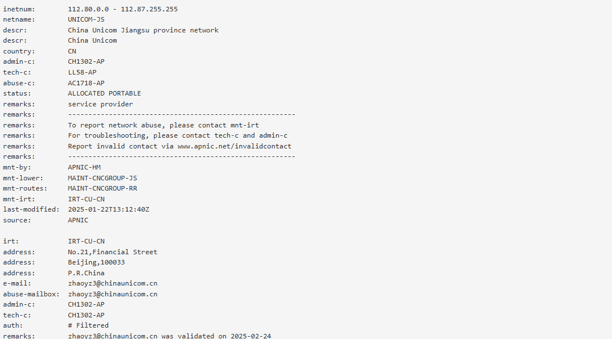
Both tools confirm that the source IP address 112.85.42.13 is based in China and tied to China Unicom Liaoning and after checking the abuse reports and comments the IP address is deemed malicious. Eventhough, in VirusTotal it, comes back as clean we know that the IP address is malicious after further investigation. The URL comes back clean but some URLs can be hidden to not be detected by software like VirusTotal. Now, lets finish on the playbook using our findings:
According to the tool Virus Total the I address 112.85.42.13 is based in China which is suspicious because it is requesting a user within our network, but let's check other sources. Remember to check more than one tool before making a determination and to complete a thorough investigation of an alert. Let's check AbuseIPDB:
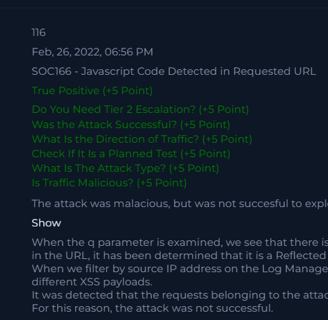
Is the alert a true positive?
A true positive.
Do you need tier 2 escalation?
No, the attack was not successful.
Was the attack successful?
No, the attack was redirected.
What is the direction of traffic?
Internet > Company Network
Check if it is a planned test
No, after checking the source/destination IPs/hostnames, URLs in emails and nothing was found to indicate that the attack was planned.
What is the attack type?
XSS
Is the traffic malicious?
Yes
In conclusion
When the q parameter is examined, we see that there is indeed an XSS payload. Since the payload is in the URL, it has been determined that it is a Reflected type XSS attack. When we filter by source IP address on the Log Management page, we see that the attacker also tried different XSS payloads. It was detected that the requests belonging to the attack were redirected with the 302 status code. For this reason, the attack was not successful. Escalation to the next level is not required as the attack is not successful.
Cyber with Zya
A collection of portfolio projects showcasing my skills in IT and cybersecurity.
zyapostworks@gmail.com
© 2025. All rights reserved.
